luogu#P9929. [NFLSPC #6] 挑战大数因子分解
[NFLSPC #6] 挑战大数因子分解
Background
NFLSPC #6 is coming soon. SolarPea, who cannot attend on-site, wants to send the std of his problem to PolarSea, who can attend.
To prevent contestants from eavesdropping on their communication to obtain the std, they plan to use a public-key encryption algorithm to ensure secure communication.
So SolarPea used an algorithm he saw on Zhihu that claims to have the “highest encryption/decryption speed and security”. Its security “depends on the hard problem of big integer factorization”:
You are a contestant with a factorization oracle, and you have already obtained the public key and the plaintext. Please use your factorization oracle to crack the std.
Problem Description
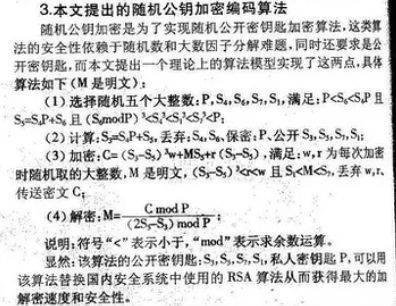
Since the image may not be clear, we restate the encryption algorithm here:
- Suppose SolarPea wants to send a message to PolarSea. They will perform the following steps.
- PolarSea first generates five big integers , such that and and $(S_6\bmod P) ^ 3 < S_4 ^ 3 < S_1 ^ 3 < (S_1 + 1) ^ 3 < S_7 ^ 3 < P$, and computes .
- Then PolarSea sends to SolarPea.
- SolarPea receives these four numbers from PolarSea. First, he needs to construct an such that , and agree with PolarSea on a method to derive from (for example, if is a relatively small positive integer, one can set ). This method is not secret, so obtaining is equivalent to obtaining . Therefore, you can ignore and only focus on .
- SolarPea generates two numbers satisfying , and computes , then sends to PolarSea.
- PolarSea only needs to compute $\frac{C \operatorname{\bmod} P}{(2S_5 - S_3) \operatorname{\bmod} P}$ to obtain .
Now you have intercepted all communications between PolarSea and SolarPea (i.e., ). Please use the known information to recover .
Input Format
The first line contains four integers , which represent the public key.
The second line contains an integer , which represents the ciphertext.
Output Format
Output one line containing an integer satisfying , which is the recovered plaintext. It can be proven that under the given constraints, is unique.
7001 4001 7 5
1155511307999246176590006
6
11083610 7305110 52 32
4578384821991465584924042474394616310820101790
39
Hint
Explanation for Sample 1
The generated values are , , , , . The computed values are , .
The plaintext is . During encryption, the chosen values are , , and the encryption result is .
Of course, this encryption is very weak this time, because is the only integer between and .
Constraints and Notes
For all data, , .
- Subtask 1 ( points): .
- Subtask 2 ( points): .
- Subtask 3 ( points): is prime.
- Subtask 4 ( points): all numbers are randomly generated.
- Subtask 5 ( points): no special restrictions.
Source: NFLSPC #6 E by asmend
Translated by ChatGPT 5
